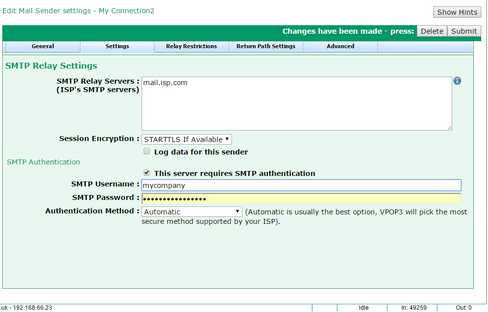
This Sender » Settings tab lets you set the options for a Mail Sender which is sending using SMTP Relay sending via another SMTP relay (Smarthost) server.
The SMTP Relay Servers box lets you enter the addresses of your Internet provider's SMTP relay servers (smarthosts). If you wish, you can enter more than one in this box - one per line. VPOP3 will attempt to connect to each server in turn until it finds one which responds, and then VPOP3 will send messages through that server. (Any SMTP errors reported by that server will not cause a subsequent server in this list to be tried).
VPOP3 will use TCP port 25 to connect to the SMTP relay servers, unless otherwise specified. To specify an alternate port, append a ':' (colon) to the server address, followed by the port number (with no spaces). For instance, to connect to smtp.myisp.com on port 587, you would use "smtp.myisp.com:587".
The Session Encryption option lets you specify whether any encryption of the connection between VPOP3 and the remote mail server should take place. There are four options:
•None - no encryption of the connection will take place.
•SSL - the connection will be encrypted as soon as it is established. This is a deprecated, non-standard, system, still used by some older mail servers. This will normally use an alternate port, often 465, although it is not standardised. This is sometimes known as SMTPS.
•STARTTLS - the connection will start off in plain text, and will switch to encrypted as soon as possible. This is the standard for SMTP session encryption. This will normally use the standard ports - 25 or 587. This is sometimes known as 'TLS'. If the remote server does not support STARTTLS encryption, VPOP3 will drop the connection and refuse to send messages.
•STARTTLS if available - the connection will start off in plain text, and will switch to encrypted as soon as possible if VPOP3 detects that the remote server supports STARTTLS. This will normally use the standard ports - 25 or 587. If the remote server does not support STARTTLS encryption, then VPOP3 will continue with the session in plain text. This option is usually the best option if you do not know whether or not the remote server supports encryption.
SMTP Authentication
The SMTP authentication options tell VPOP3 how to log in to your Internet provider's SMTP relay server to send messages.
Unlike POP3 & IMAP4, authentication in the SMTP standard is optional. Some Internet providers will not require authentication, instead only allowing access from IP addresses which are recognised.
If your Internet provider does require authentication, then check the This server requires SMTP authentication box, then in the SMTP Username and SMTP Password boxes, enter the relevant login details provided by your Internet provider (these are often the same as those used for collecting mail from the Internet provider).
The Encryption Method option lets you specify which authentication method VPOP3 will use for logging onto the remote server. Usually Automatic is the best option, as VPOP3 will pick the most secure method supported by both VPOP3 and the remote server.
VPOP3 supports two authentication methods:
•Plain text - the username & password are sent as plain text (if you look in the logs or monitor the TCP/IP traffic it may look encrypted, but it is a Base64 encoding of the plain text, so is easy to convert back to plain text).
•CRAM-MD5 - the username is sent in plain text, but the password is encrypted using a challenge-response one way hash encryption system. Using this system, the original password is hard to recover from the transmitted data, and it is virtually impossible to use a 'replay attack', so this is more secure than the plain text method. However, some mail servers report that they support CRAM-MD5 authentication, but their implementation is broken, so this may not work, and you may need to manually select the "Plain text" method.
Note that passwords are sent after any Session Encryption has been established, so if the session is encrypted, it is safe to use plain text passwords as the password will still be encrypted by the session encryption.